最新消息
了解更多 XCockpit 核心應用
為什麼你的 Active Directory 防護無法成功阻擋駭客?
長久以來,Windows Active Directory (AD) 做為廣受採用的身份驗證與管理工具,掌管著企業網路場域許多重要關卡的鑰匙,然而其悠久的歷史與高度複雜性,卻也無可避免地導致了許多易被攻擊的弱點與漏洞。
了解更多
客戶案例-政府 A 級機關:經濟部
如何在攻擊發生前掌握資安防禦與事件應變能力? 如何在沒有任何攻擊事件、且不影響日常營運的前提下測試與評估保護措施的有效性?
了解更多
揭秘針對臺灣金融單位的供應鏈攻擊手法
2022 年到 2023 年間,在我們監控範圍下的許多金融單位,均能觀察到中國駭客組織的攻擊行為,比起往年顯得更加活躍;而藉由相關的調查,我們也發現了其中許多攻擊的成因,都與供應鏈相關的資安問題習習相關。
了解更多
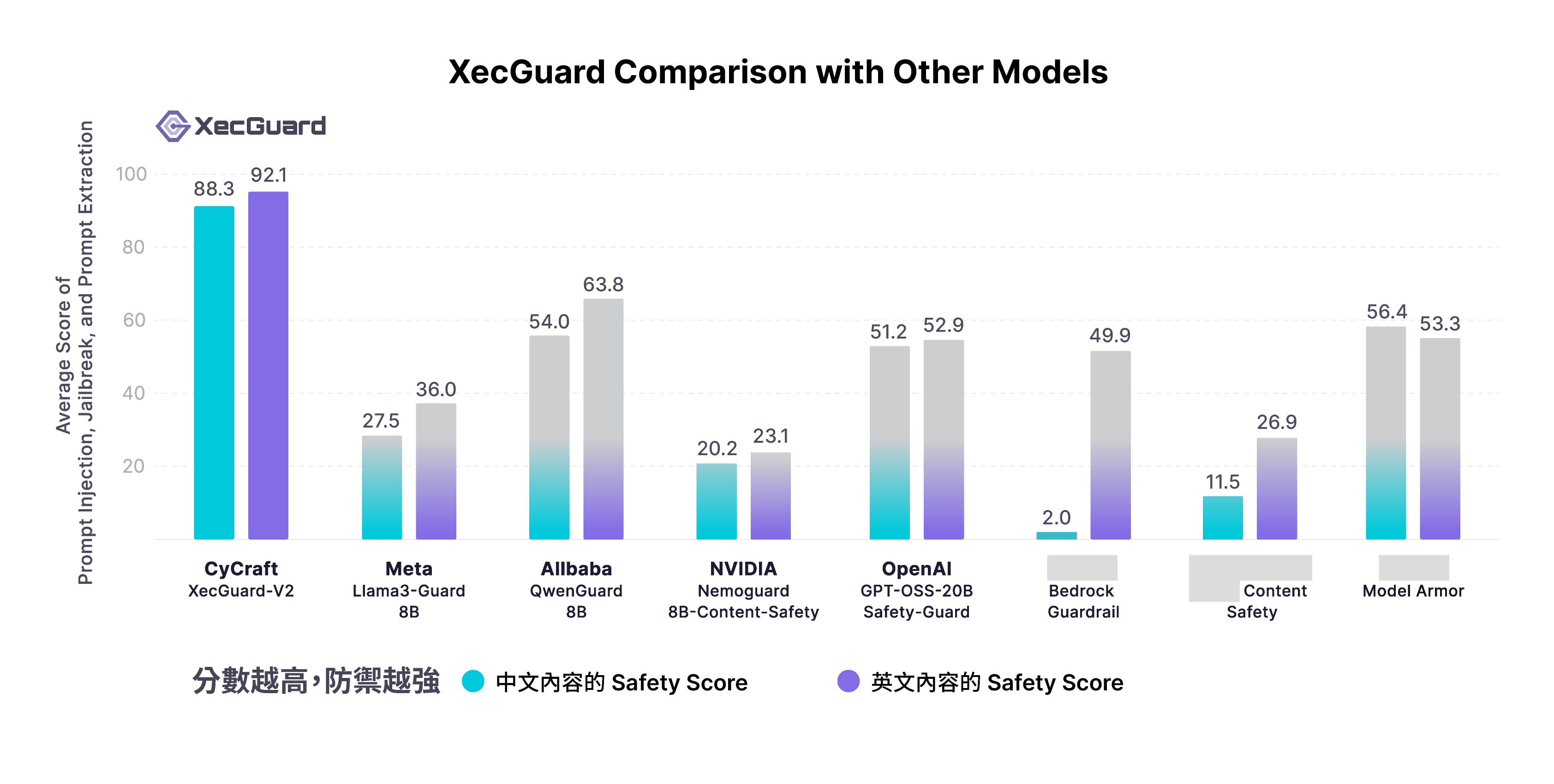
國際研調認可

AI 賦能的奧義資安服務
進一步了解 XCockpit 自動化威脅曝險管理平台的服務範疇
Thank you! Your submission has been received!
Oops! Something went wrong while submitting the form.