[Originally Published by ScanNetSecurity Japan] Boosting Digital Forensics Productivity by 2x to 4x: CyCraft Japan Addresses Market Shortages with AI Forensics
This article is translated from a report by the Japanese cybersecurity media ScanNetSecurity: 〈デジタルフォレンジック調査の生産性を 2 倍から 4 倍に ~ CyCraft Japan、AI フォレンジックで日本市場の供給不足解消へ〉. For the original Japanese report, please refer to ScanNetSecurity, published February 25, 2026.
A sense of helplessness is spreading among service providers on the front lines of Incident Response (IR).
Sangwook Kang, Country Manager of CyCraft Japan, the subsidiary of CyCraft, points out: "IR service providers have the technology and the talent. Yet, they can only handle a tiny fraction of the digital forensics requests from enterprises hit by cyberattacks."
In reality, it has become common for major cybersecurity firms to decline forensic investigation requests, responding with: "We are currently at full capacity," or "Please wait until next month—or even six months from now."
The reason for this bottleneck is clear: a traditional digital forensics investigation requires an average of one week to analyze a single device. No matter how skillful the technician is, there is a limit to how many projects one person can manage simultaneously. Consequently, an IR service provider can handle a maximum of about 50 cases per year. In Japan, where cyberattacks have become a daily occurrence, demand continues to surge while supply remains stagnant and difficult to scale. This structural contradiction places immense pressure on enterprises suffering from ransomware and other similar attacks.
Kang is determined to fundamentally change this landscape: "I want every enterprise providing IR services to use CyCarrier as their default tool." Currently, he is leveraging the AI-driven digital forensics tool CyCarrier to establish a new industry standard for the Japanese IR market.

The Structural Limits of Digital Forensics
“Digital Forensics” refers to the root-cause investigation and scope of impact after a cyberattack. Only after confirming the attack path and understanding the full extent of the damage can an enterprise develop strategies to prevent recurrence and fulfill its accountability to partners or regulatory sectors.
However, traditional forensic methods have reached their limits. First, the hard drive must be removed from the compromised device to create a complete disk image using specialized equipment (taking about half a day). Subsequently, professional tools such as EnCase or FTK are used for analysis (at least one day or more) to reconstruct the attacker’s movements. Each device takes approximately one week, and the costs for large-scale investigations—ranging from tens of millions to over 100 million yen—are not uncommon.
Another fundamental issue is that a "full-endpoint investigation" of an attacked organization is practically impossible under current conditions. If 1,000 devices each required a week of investigation, it would theoretically take 19 years to complete. Even if conducted simultaneously, the time and cost remain astronomical. As a result, companies can only select a few of the most suspicious devices for investigation, leaving the rest of the fleet outside the scope of analysis.
The most critical issue is the talent shortage. The number of forensic technicians is severely insufficient. Even when commissioning specialized firms, clients are frequently told that "manpower is currently unavailable" or that "a wait of several months to half a year is required."
Kang notes: "As long as investigations remain human-centered, the number of projects a single technician can handle is still limited. This creates a structure where revenue cannot grow even as demand increases, simply because firms cannot take in new orders."
Changing the Speed and Scope of Forensics with AI
CyCarrier, developed by CyCraft, is designed specifically to break these structural constraints.
The defining feature of CyCarrier is its ability to drastically increase investigation speed. According to a white paper by Frost & Sullivan, a top-four global fabless semiconductor company implemented CyCarrier during a pre-acquisition security audit. An investigation that would have normally taken months was completed in just a few days—reducing investigation time by over 99% and cutting costs and labor by over 95%.
The key to achieving this speed lies in the AI technology that CyCraft has invested in since its founding. Today, attackers have begun using AI to launch strikes; naturally, defenders have also begun using AI. However, there is one area where AI has yet to fully penetrate: IR and Post Forensics.
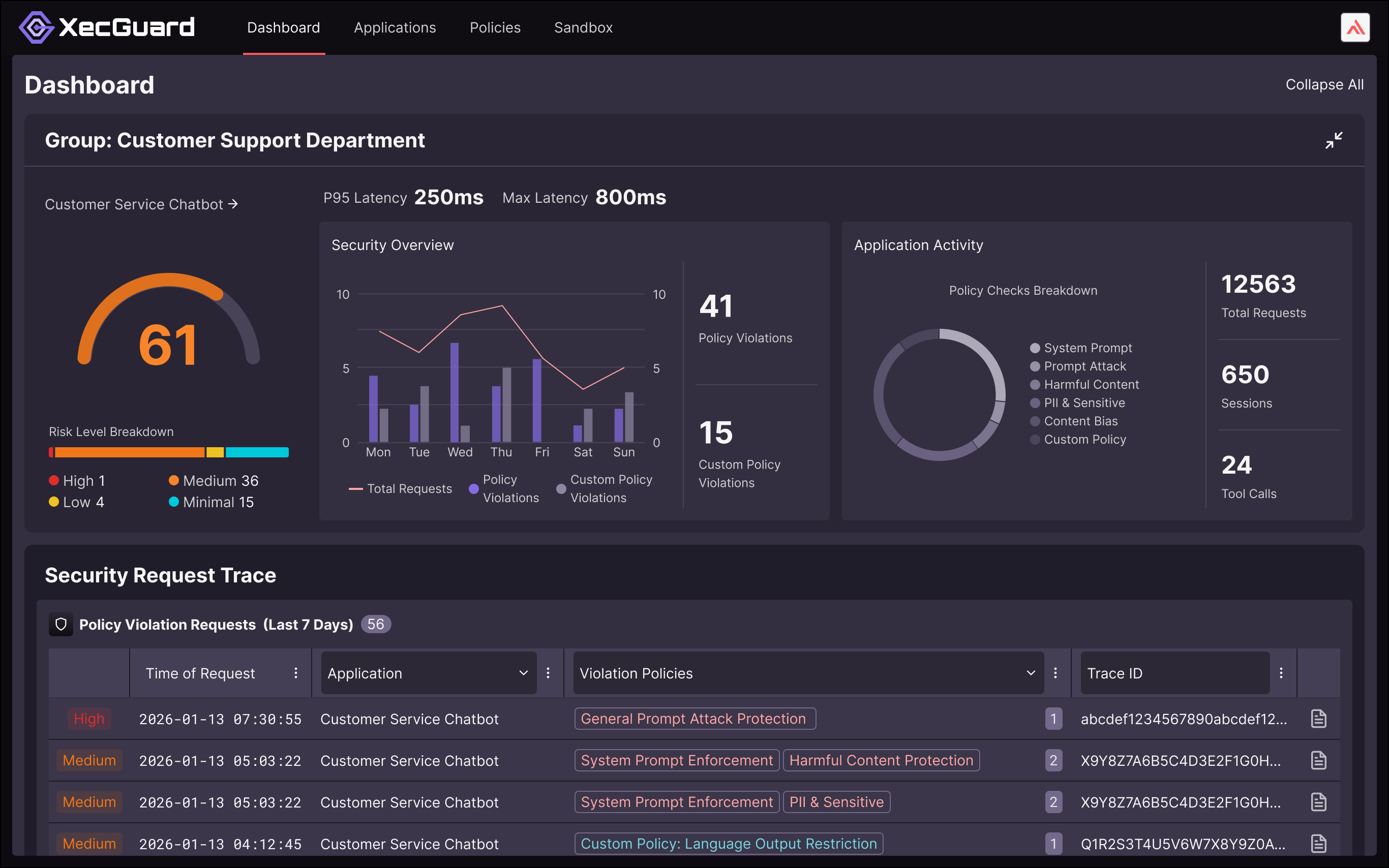
CyCarrier automatically collects information from all endpoints, uses AI to perform prioritization and analysis, and finally presents the data for technicians to make the ultimate judgment. This is not merely an efficiency gain; it is a proposal for a "new method of forensics."
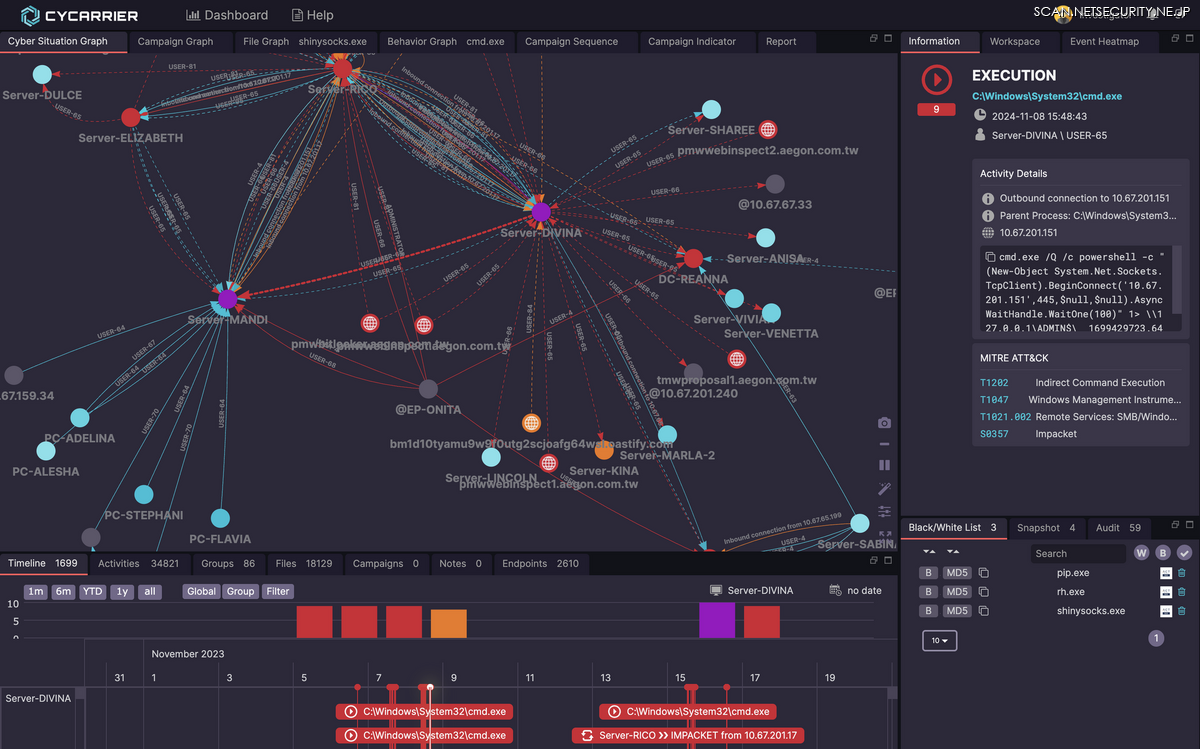
In one corporate investigation case, CyCarrier scanned a total of 2,456 devices and analyzed 81,517,371 files. The entire investigation took 19 days. If the same scale of investigation had been conducted using traditional methods, it would have theoretically taken 47 years (1 week × 2,456 devices = 17,192 days ÷ 365 = 47.1 years). Amidst this massive data set, CyCarrier ultimately identified 41 truly high-risk devices, representing only about 1.7% of the total fleet.
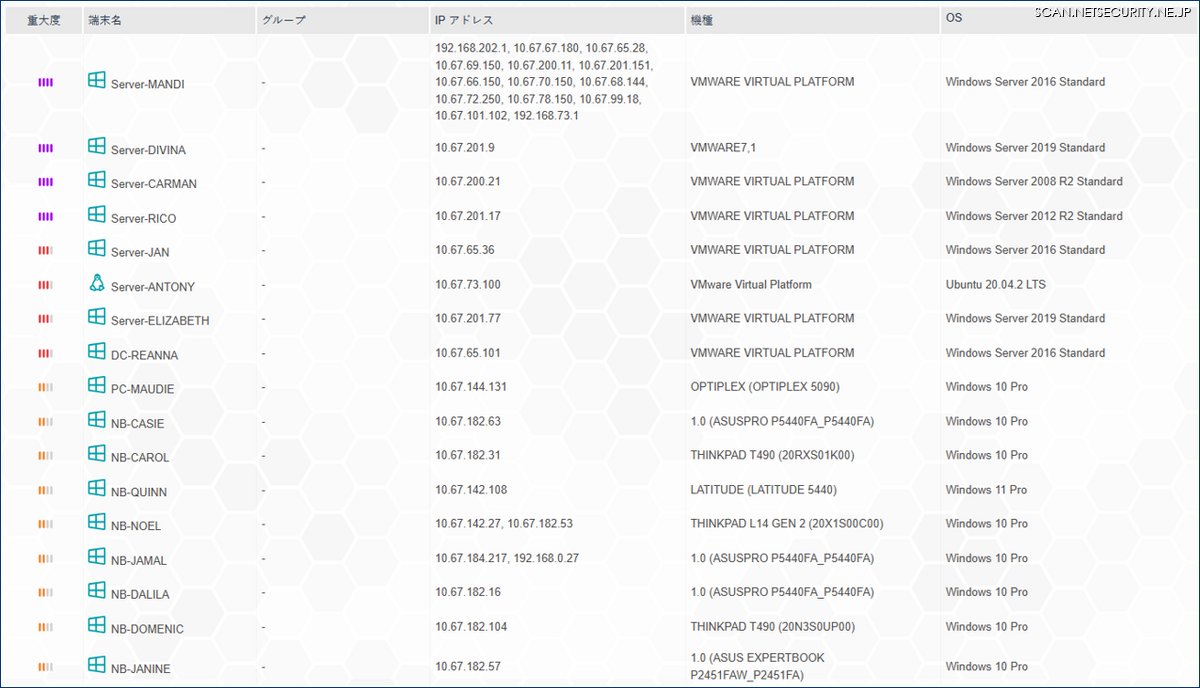

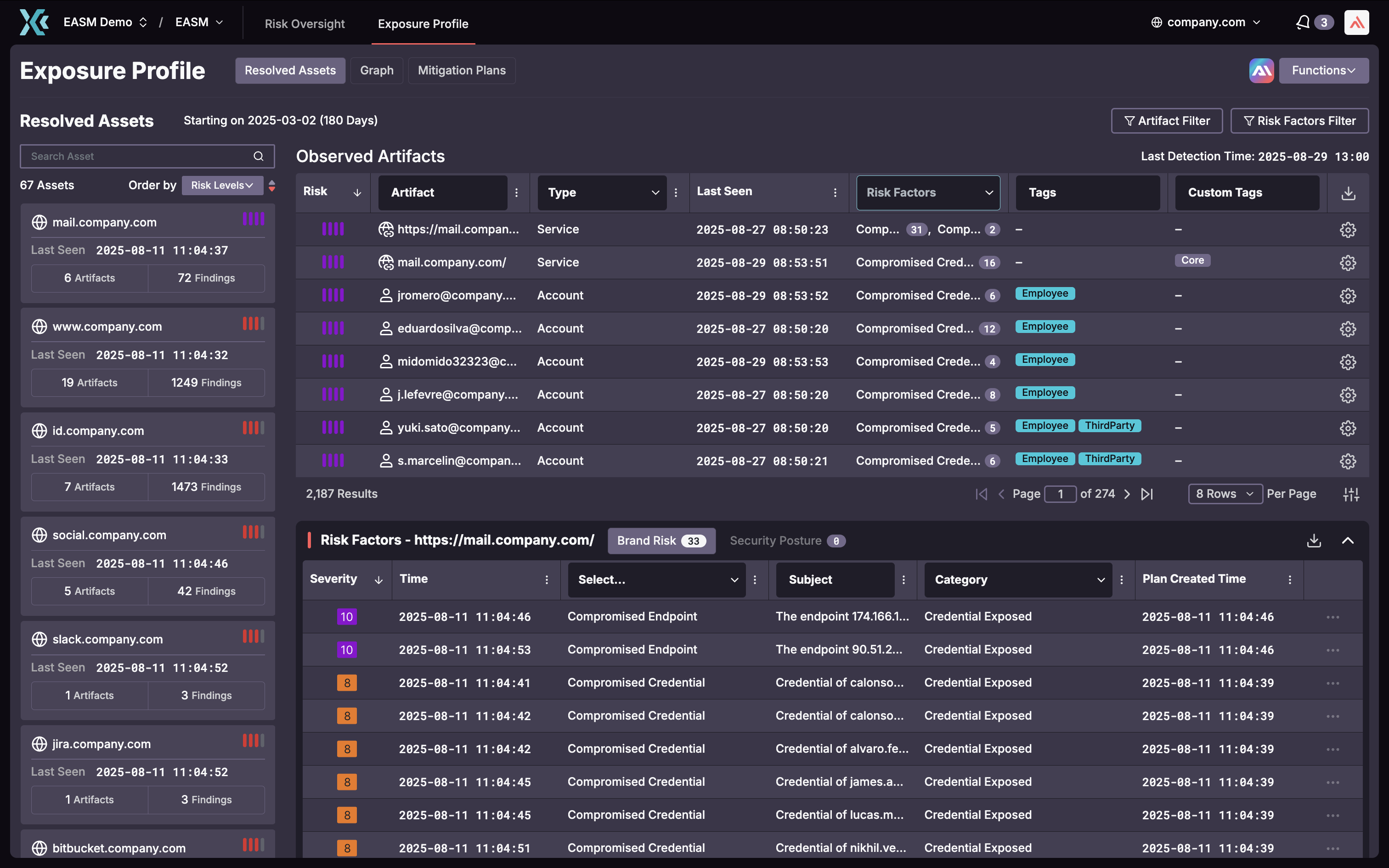
Another differentiating advantage of CyCarrier lies in its ability to retrospect. While many EDR (Endpoint Detection and Response) solutions can only collect data generated after their installation, CyCarrier performs a daily automated scan to gather various logs natively recorded by the Windows system—such as Event Logs, Registry, and Prefetch. Consequently, even traces of attacks that occurred prior to deployment can be visualized, provided they remain within the Windows retention period (typically ranging from several days to weeks, depending on the case).
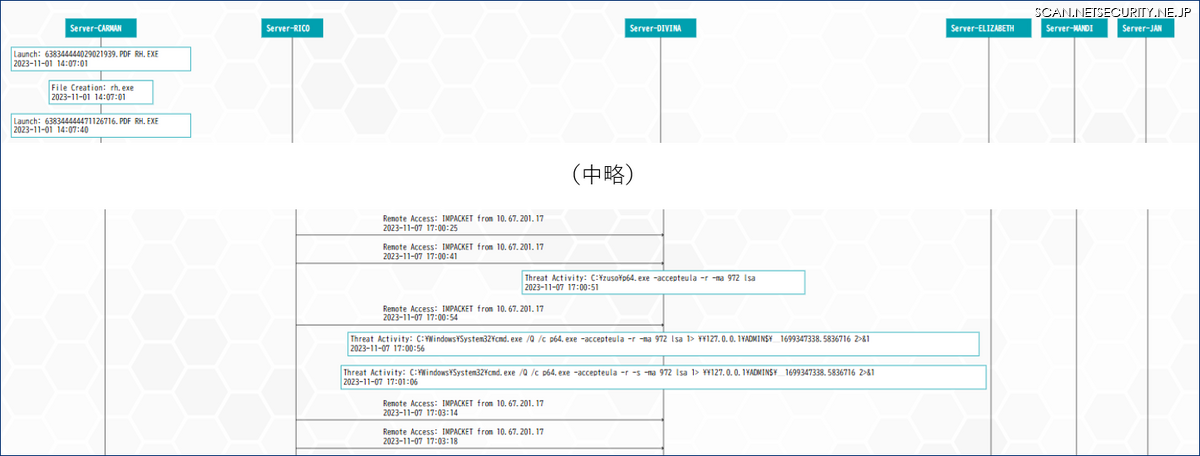
Furthermore, CyCarrier automates the visualization of attack paths, a task that previously required manual effort by highly skilled technicians. The platform clearly illustrates where an intrusion began and how it moved laterally through the network using a diagram that resembles, at least to the reporter, a “ladder-climbing game" chart. This visual diagram includes timeline, executed commands, and mapped MITRE ATT&CK® techniques, serving as an invaluable resource for briefing executive management during ransomware incident responses.
Two Strategic Proposals for the Japanese Market
Sangwook Kang’s strategy for the Japanese market is built upon two core pillars:
The first strategy involves providing CyCarrier to cybersecurity firms that offer IR and forensic investigation services. "If a firm could only handle 50 forensic investigations a year in the past, using CyCarrier makes it possible to process 100 or even 200 cases," Kang explains.
CyCraft adopts a B2B2B business model, opting to provide technology to security firms rather than selling directly to end-users. Its primary value proposition is a 2x to 4x increase in productivity for IR service providers. By doubling or tripling existing forensic capacities, the market’s supply shortage can be alleviated, reducing the number of victimized enterprises left stranded without available investigators.
CyCarrier also maintains high price competitiveness. According to JNSA (Japan Network Security Association) surveys, forensic costs typically range from 1 million to 2.2 million JPY per PC. In contrast, a one-time CyCarrier license for 1,000 devices is priced at approximately 3.6 million JPY (Partner Price). Furthermore, the investigation duration is drastically shortened to between three days and one week, compared to traditional methods.
Kang’s goal is clear: "I want every firm providing IR services in Japan to use CyCarrier as their default tool," effectively establishing it as the industry standard.
The second strategy targets major corporations that maintain their own internal teams of two to three IR experts. CyCarrier is offered to these organizations through specialized service contracts. Currently, a major manufacturing firm with approximately 40,000 employees is planning implementation. Interestingly, they intend to use the tool not just for post-incident investigations, but as a regular monthly or quarterly security "health check." This represents a "preventative medicine" model of security operations—identifying threats before a full-scale attack occurs.
The Competitive Edge of Taiwanese Enterprises
With over 26 years of experience in the IT industry, Sangwook Kang has served as President or Country Manager for various global cybersecurity leaders, including Symantec, Radware, and AhnLab, navigating diverse corporate cultures and geopolitical backgrounds. Today, he represents the Taiwanese firm CyCraft Japan in its mission to expand within the Japanese market.
Kang believes each region has its strengths: "South Korea, the U.S., and Israel all have unique advantages. However, Taiwan’s specific edge lies in its unparalleled experience and technical expertise in defending against China-linked cyber threats."

A significant proportion of cyberattacks targeting Japanese enterprises originate from China. Due to geopolitical factors, the Taiwanese firm CyCraft maintains a continuous flow of high-level APT intelligence—threats backed by massive budgets and cutting-edge technology.
Benson Wu, CEO and Co-founder of CyCraft, once remarked in a ScanNetSecurity interview: "In Taiwan, we can just sit here and receive a massive volume of high-end cyberattack data to train our AI—and it's all for free. So, our AI security products will only get better. It’s great, right?" As he said this, he flashed an innocent, boyish smile. It was an exceptionally optimistic, perhaps even overly bold statement, yet it left a lasting impression.
The results of these product refinements have already been validated. In a 2020 global evaluation of 21 products based on the MITRE ATT&CK® framework, CyCraft achieved the highest score in detection capabilities. Furthermore, CyCraft consistently presents its research via CFP (Call for Papers) at prestigious international cybersecurity conferences such as Black Hat USA and CODE BLUE.
When asked about the competition, Sangwook Kang states firmly: "I believe no other security vendor in the world possesses the same technology."
Currently, CyCraft is expanding its partnerships with existing collaborators, such as Digital Data Solution Inc. (デジタルデータソリューション株式会社). While specific company names cannot be disclosed at this time, it is understood that approximately three to five major cybersecurity firms—including some frequently mentioned in this magazine—are currently evaluating the implementation of CyCarrier. Whether this technology truly is "without peer in the world" as claimed is currently being verified by these organizations.
ScanNetSecurity does not unconditionally endorse the idea that "all IR firms should use CyCarrier by default." However, even if Kang’s vision is only partially realized, one thing is almost certain: the number of enterprises suffering from ransomware-induced business halts—yet struggling to find available forensic investigators—will decrease. That much is a certainty.
Original text by Junya Takahashi
About CyCraft
CyCraft is a cybersecurity company founded in 2017, focusing on autonomous AI technology. Headquartered in Taiwan, it has subsidiaries in Japan and Singapore. CyCraft provides professional cybersecurity services to government agencies, police and defense forces, banks, and high-tech manufacturers throughout the Asia-Pacific region. It has received strong backing from the CID Group and Pavilion Capital, a Temasek Holdings Private Limited subsidiary.